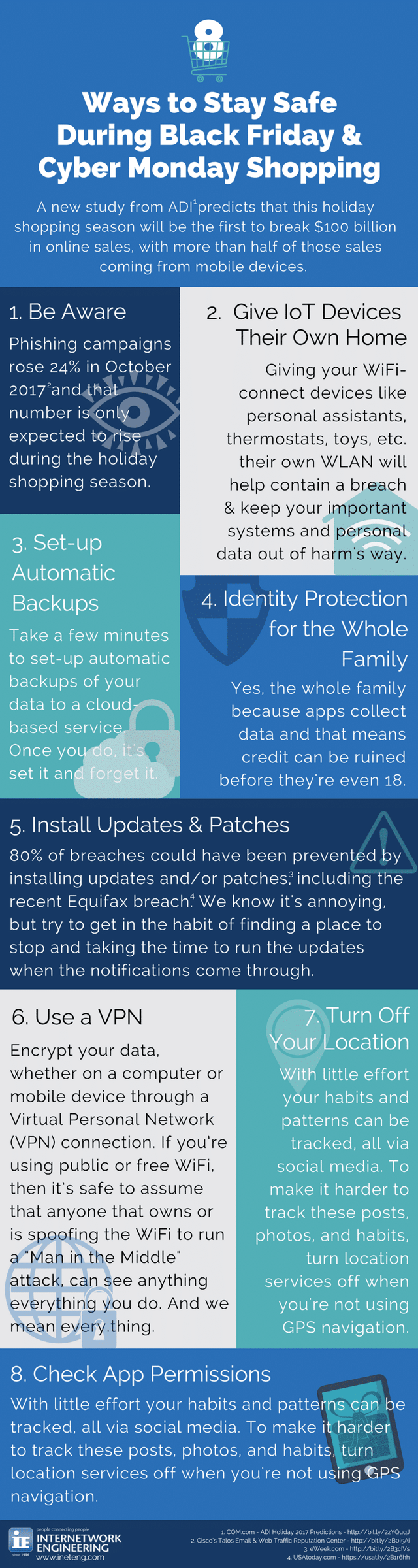
8 Ways to Stay Safe During Black Friday & Cyber Monday
The holiday season means holiday shopping and while everyone will be looking for a bargain, it’s important to make sure you don’t get something you weren’t bargaining for. A new study from ADI predicts that this holiday shopping season will be the first to break $100 billion in online sales, with more than half of those sales coming from mobile devices.
Here are some online shopping safety tips:
1. Be Aware
There’s going to be phishing and spear phishing campaigns leading up to Black Friday and well past Cyber Monday. There’s no way to get around it.
What are phishing and spear phishing campaigns? Phishing campaigns are blanket spam emails sent out in large numbers, hoping to tempt unknowing and naïve end-users into clinking on a dubious link. Spear phishing is a more targeted attack, but both types of campaigns look to lead the victim to their malicious code.
These spam messages will also show up in social media, cell phone applications, and as links within Google searches, such as the Zeus Panda popping up in the last few weeks. The best way to visit new or unknown sites is to go directly to the destination site and search within that site for the needed content.
Information from Cisco’s Talos Email & Web Traffic Reputation Center shows an increase in the number of these phishing campaigns in the last month, and we’ll be sure to see even higher numbers as we roll into the holiday shopping seasons. These are the most recent numbers:
- Average daily spam volume for October 2017: 454.61 Billion
- Spam volume change from previous month: +24%
2. Give your IoT (Internet of Things) devices their own home network
This recommendation may take a little more effort than just having better email hygiene. As we connect more WiFi enabled devices, such as washers, toasters, refrigerators, toys, wearable devices, and intelligent personal assistants, to our networks, it's important to keep in mind that these devices, if compromised, would be better contained if they had their own dedicated wireless network. This will keep any breach separated from your important systems or data.
3. Set up automated backups
There are several ways to set up automated nightly backups to a cloud-based service, and it’s worth every bit of effort to so. This way, if your data is corrupted or falls victim to ransomware or the next day zero attack, you’ll only be out of one day’s worth of data.
- Apple users (mobile and computer based) can take advantage of the iCloud
- Android mobile users (as well as PC users) can take advantage of Google Backup and Sync.
- And if you don’t like either of those, more options can be found in this article from TechRadar.
4. Invest in Identity Protection for the whole family
Yes, the whole family, including those under the age of 18. You might think, why would I need to do this when my kids are not of age to worry about identity theft? Most kids easily have 10 times more online accounts than adults, ranging from social media to the latest must-have app. These apps, even the seemingly harmless ones, are known for collecting personal data. Data that could easily be used to open credit card accounts and ruin your children’s credit before they even apply for their first credit card.
Not sure where to start? Check out this list from Consumers Advocate.
5. Learn from Equifax and install all updates and patches.
Did you know that 80% of breaches could have been prevented by installing updates and/or patches? This includes the recent Equifax breach.
We get it, it’s annoying to be in the middle of a project and have an update notification pop-up. It’s also very easy to dismiss that notification under the false belief that you’ll actually follow through with the update when you select “remind me tomorrow.” Instead, try to get in the habit of finding a place to stop and taking the time to run the updates when the notifications come through. This will make sure your computer and any possible software “holes” are taken care of immediately and save you more headache in the long run.
6. Use a VPN (Virtual Personal Network)
If you don’t want your data visible to potential unwanted viewers, then you need to encrypt your data through a VPN connection. If you’re using public or free WiFi, then it’s safe to assume that anyone that owns that WiFi, or someone spoofing that free WiFi and running a “Man in the Middle” attack, can see anything and everything you do. And we mean any.thing.
If you’re using a company computer, laptop, or mobile device, you should have a company-issued VPN installed. If you aren’t sure where to find it or how to use it, contact your IT department.
If you’re using your personal computer, laptop, or mobile phone, there are plenty of options out there for you. Check out this list of top VPN providers from PC Magazine.
7. Turn off location services if you aren’t using GPS
This is never an easy discussion, but reality is not always an easy button discussion. There are known and unknown predators out there and it’s our responsibility to protect our family and loved ones from the threats they present. Criminals have always used technology to their advantage or to gain an advantage. With little effort and research, these predators can track the habits and patterns with surprising accuracy, all via social media tweets, Instagram photo posts, and other various social platforms. To make it harder to track these posts, photos, and habits, turn GPS location services off.
Unfortunately, some applications don’t make it easy for you to do this, or make you think you don’t have an option – but you do.
- Here’s how to disable location services for Apple devices.
- Here’s how to disable location services for Android devices.
And if you ever get a pop-up asking for a website to use your location, just deny it.
8. Check app permissions
This may sound strange, especially if you’re the only one using a computer, but it’s is always a good habit to NOT have your default account or user account assigned with Admin privileges. This can act as a prevention method to prevent malicious software from having the ability to install itself onto your device. All you have to do is create a separate user account for your computer, and log in under that from here on out.
On your mobile, always make it a practice to review the default app permissions via your mobile device’s system settings. This will make sure that the app only has the permission to do the things you want it to do and not the things you don’t, like access your photos, microphone, and location services.
The holiday shopping season is a great time of year but don’t let your emotions get the best of you, if you think it’s too good to be true, it most likely is. If you’d like more information about how IE can help your customers shop safely on your networks or how your business can increase its security in general, reach out! One of our security team members would be happy to chat with you.
Share the infographic to easily help your friends and family stay safe!
(Click to make larger or download the PDF.)
About the Author:
Derrick Whisel has worked in IT for over 20 years, with extensive experience in project engineering, management, scoping, budgeting and design. He began his career in the military, and after being honorably discharged as an IT2 Second Class Petty Officer, moved into the private sector where he now works as a Security Solutions Specialist for Internetwork Engineering.
About Derrick Whisel
Derrick Whisel has worked in IT for over 20 years, with extensive experience in project engineering, management, scoping, budgeting and design. He began his career in the military, and after being honorably discharged as an IT2 Second Class Petty Officer, moved into the private sector where he now works as a Senior Technical Advisor for Security Solutions here at Internetwork Engineering.